You shouldn’t have to choose between protecting your data and managing your caseload.
General purpose workflow tools make it easy to share information and communicate across your organization. But they’re not so great at handling confidential information. The Yakabod platform is designed with a security-first architecture to support teams that manage highly sensitive investigations, incidents, and cases. Our customized (and customizable) applications help you save time while protecting your data.
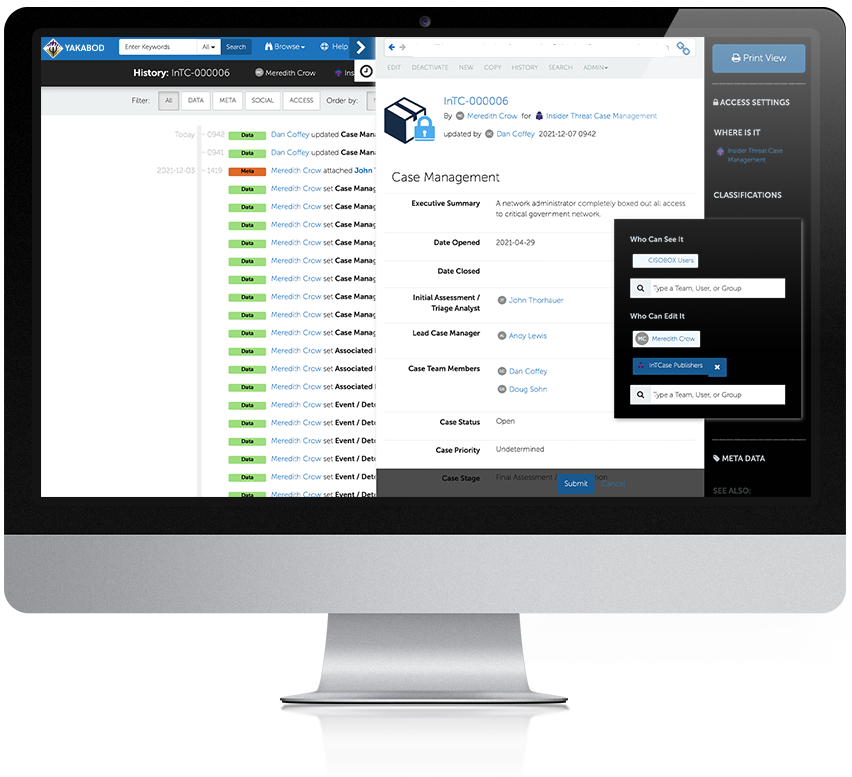
Security isn’t something you can add when you need it. That’s why we baked it in from day one. Yakabod includes granular access controls, a hardened appliance, and system-of record capability with every deployment.

Yakabod’s secure case management platform was originally developed for the highest-security intelligence environments in the world. Now we’re using that same technology to empower business leaders, higher education institutions, and government agencies. Yakabod consistently meets the highest standards for product security.